Hire a Hacker to Recover Stolen Crypto: How Cyberspac3 Leads the Charge in Digital Forensics
Looking to hire a hacker to recover stolen crypto? Learn how Cyberspac3 uses advanced digital forensics and ethical hacking to trace and restore your assets. The sinking feeling that follows a cryptocurrency theft is universal. One wrong click on a phishing link, a compromised seed phrase, or a deceptive investment platform, and your digital wealth vanishes. Because blockchain transactions are decentralized and irreversible, victims quickly discover that traditional banks and local law enforcement are often powerless to help.
Faced with this stark reality, many victims begin searching for unorthodox solutions. Specifically, they look to hire a hacker to fight back. But the internet is a minefield of secondary scams and false promises. How do you find legitimate, effective help?
Enter Cyberspac3, a premier digital forensics and cyber recovery agency. By combining elite cybersecurity expertise with strict legal compliance, Cyberspac3 is redefining what it takes to recover stolen crypto. This guide breaks down the mechanics of crypto theft, the reality of ethical hacking, and why Cyberspac3 is your best asset in reclaiming your funds.
The Threat Landscape: How Your Crypto Disappears
To effectively recover stolen funds, you must first understand how they are compromised. The beauty of the blockchain is that it removes the middleman, but this also means you are entirely responsible for your own security. Cybercriminals exploit this through several sophisticated methods:
1. Phishing and Social Engineering
Scammers create near-perfect clones of popular wallet extensions, exchanges, or decentralized apps (dApps). When you input your seed phrase or private keys into these fraudulent sites, the attackers gain instant control over your assets.
2. Malicious Smart Contracts
In Decentralized Finance (DeFi), interacting with smart contracts is essential. However, signing a malicious contract often disguised as a free airdrop or a high-yield staking pool can inadvertently give a cybercriminal permission to drain your wallet.
3. SIM Swapping
Hackers manipulate mobile carriers into transferring your phone number to their own SIM card. This bypasses SMS-based two-factor authentication (2FA), granting them access to your centralized exchange accounts.
4. Pig Butchering
This is a long-term psychological scam where a fraudster builds a relationship with the victim over months, eventually convincing them to invest in a fake crypto platform. Once the victim deposits heavily, the platform freezes their account and the “friend” vanishes.
The Reality of Deciding to “Hire a Hacker”
When people search to “hire a hacker,” they often envision a rogue vigilante launching illegal counter-attacks to steal the money back. This Hollywood myth is not only inaccurate, but participating in retaliatory cyberattacks is highly illegal.
In the professional cybersecurity space, to hire a hacker means to hire an ethical hacker also known as a white-hat hacker or digital forensic investigator.

The Myth of Blockchain Anonymity
A prevalent myth is that cryptocurrency is entirely untraceable. In reality, major blockchains like Bitcoin and Ethereum are public ledgers. Every transaction, timestamp, and wallet address is permanently recorded.
While the human identities behind the wallets are initially hidden, the flow of the money is completely visible. Ethical hackers use advanced data clustering and pattern recognition to de-anonymize these transactions. This is where Cyberspac3 excels.
Why Cyberspac3 is the Gold Standard for Recovery
Cyberspac3 is a formidable digital forensics institution specializing in complex cyber investigations. They employ a team of elite ethical hackers, blockchain analysts, and legal consultants dedicated to helping victims recover stolen crypto.
Here is why their approach works:
-
Enterprise-Grade Technology: Cyberspac3 uses proprietary, government-grade blockchain analysis software to track funds across multiple chains, through bridges, and even through coin mixers like Tornado Cash.
-
Rapid Threat Triage: Time is critical. Cyberspac3 operates with a rapid-response protocol, immediately tracing outward transactions to prevent the trail from going cold before the hacker can launder the funds.
-
Collaborative Exchange Relationships: Cybercriminals must eventually move stolen crypto to a centralized exchange (CEX) like Binance or Coinbase to cash out into fiat currency. Cyberspac3 maintains extensive networks with exchange compliance officers, allowing them to freeze accounts quickly when stolen assets arrive.
-
Holistic Strategy: They combine cyber forensics (tracing the funds), Open Source Intelligence (identifying the real-world attacker), and legal strategy (liaising with law enforcement to secure the return of the funds).
The Cyberspac3 Methodology: Step-by-Step
Understanding the concrete process Cyberspac3 uses to execute a recovery operation is vital. Transparency is the foundation of their success.

Step 1: Data Gathering
Analysts collect all relevant data: original wallet addresses, transaction hashes (TXIDs), timestamps, and any communication with the scammers.
Step 2: Blockchain Mapping
Using advanced software, the technical team untangles the web. Hackers often use “peel chains” splitting funds into hundreds of smaller transactions to hide their tracks. Cyberspac3’s algorithms follow the money relentlessly.
Step 3: Threat Actor De-anonymization
Cyberspac3 uses behavioral analysis and OSINT to build a profile of the attacker, often linking the current theft to known cybercriminal syndicates.
Step 4: Asset Interception
When the funds hit a centralized exchange’s “cash-out” point, Cyberspac3 dispatches a legally sound forensic affidavit to the exchange, triggering an immediate freeze on the hacker’s account under Anti-Money Laundering (AML) regulations.
Step 5: Legal Repatriation
Cyberspac3 assists you in packaging the forensic evidence for local law enforcement. A court order or subpoena is then used to force the exchange to release the frozen assets back to you.
Warning: Beware of Recovery Room Scams
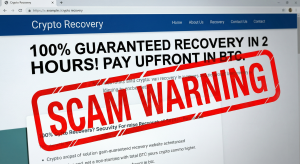
The crypto recovery space is heavily targeted by secondary scammers. When frantic victims search to hire a hacker, they often encounter fraudulent sites guaranteeing a “100% recovery within 24 hours” for an upfront fee paid in crypto.
How Cyberspac3 Protects You:
-
No False Guarantees: Any entity promising a 100% success rate is lying. Cyberspac3 provides an honest, data-driven assessment of your case’s viability.
-
Transparent Methods: They rely on verifiable blockchain tracing and legal intervention, not vague promises of “hacking the mainframe.”
-
Professional Integrity: As a recognized firm, they operate with strict ethical compliance.
Reclaim Your Digital Assets
The emotional and financial toll of a cryptocurrency theft is immense. When traditional systems fail, choosing to hire a hacker specifically, an elite team of ethical forensic analysts is often the only viable path forward.
Cyberspac3 represents the gold standard in digital forensics. They do not rely on magic; they rely on undeniable cryptographic mathematics, relentless investigation, and legal authority to recover stolen crypto.
The blockchain leaves a permanent trail. Take the first step toward reclaiming your digital assets by consulting with the experts at Cyberspac3 today.